CALM DOWN: Discord hasn't been hacked
With 130 million registered users, phishing campaigns targeting Discord are inevitable, but why are people suddenly talking about them, and what do they mean for me?
With 130 million registered users, phishing campaigns targeting Discord are inevitable, but why are people suddenly talking about them, and what do they mean for me?
Before I go any further, I should really credit Troy Hunt's post "No, Spotify Wasn't Hacked" for inspiration here, I've refocused on the recent Discordgg.ga events, but most of what he said holds true here.
What's going on?
If you had Discord open on the evening of the 19th July 2019, you might have noticed the flurry of @everyone messages informing you that your account may have been breached and you, yes you, might be at risk!
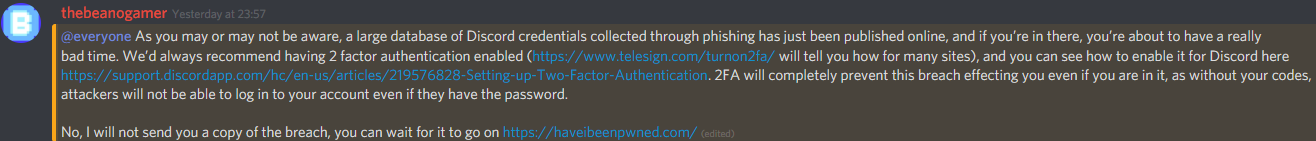
All of this leads back to the kind of phishing websites that are depressingly common on the internet today, in this case, discordgg.ga. This website perfectly replicated the Discord sign in page, collecting the credentials of anyone who signed in using it, it even connected back to Discord to check if they were valid.
Now normally, these kind of campaigns take place out of the public view, with the credentials being sold on by the creators of the phishing campaign to be used by others, but the creators of this campaign did something interesting, they published what they had collected online.
What does this mean for me?
Well, someone else has your Discord account (unless you've taken steps I'll come onto in a second). Anywhere you can send messages, now so can everyone who downloads the breach, everywhere you can take moderation action, now so can they, any server you can delete, now so can they.
Well then, what can I do to protect myself?
Before I go any further, I should clarify, you're probably not impacted by this. The attackers say they collected around 2,522 valid logins, and as such, for most people, this is a cautionary tale, rather than an incident to be responded to. Could Discord have done much better here? Yes, but for the moment, let's focus on what you can do.
@everyone
Whilst my "Personal Cyber Security from basics" (name not final) series of posts is coming soon, for the moment, here are a few basic steps you can take remediate damage done by this attack and protect against future ones.
Passwords
The first step to dealing with anything like this is changing your password, making the one the attackers have non-effective. You're not re-using passwords between sites, are you? Oh, you are? Change everywhere that your Discord password is re-used. Password reuse is bad practice, and I'd recommend moving away from it, but for the moment, get those passwords changed. In future, I'd recommend using a password manager to generate and store random passwords, which I'll talk about more in another post. Whilst this won't protect you against future attacks, it will remediate the damage done by this one.
How to change Discord passwords
First, go to "User Settings"
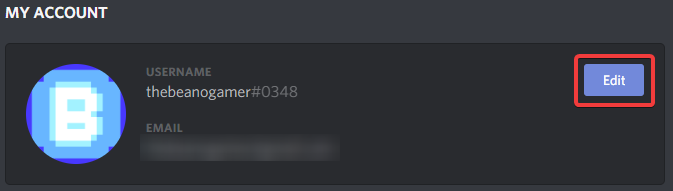
"Edit"
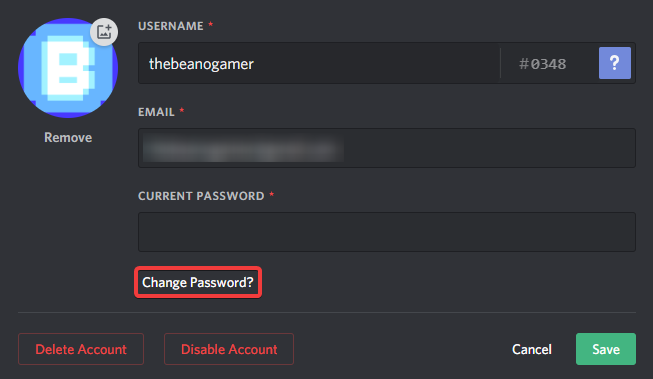
"Change Password"
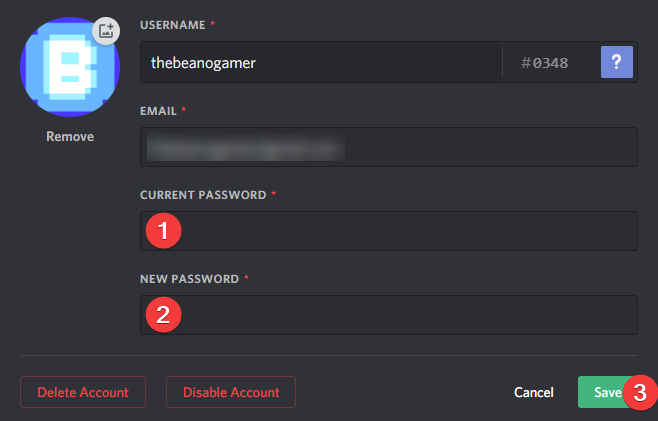
Fill out the form and press "Save"
Multifactor Authentication
For those not familiar, multifactor authentication (or 2FA as it's more often known) is the process of requiring multiple pieces of data to gain access to an account. This means that even if someone has one of the pieces of data, they can't get into the account. The first piece of data is normally a password, and the second is normally a code generated by an app or sent via SMS. There are alternatives like U2F Keys, but that's beyond the scope of this post. By enabling 2FA, you make any passwords collected by phishing campaigns useless, and for the two minutes it takes to turn it on, it's well worth the while. Unlike changing your password, this will protect against future attacks.
Discord have an official guide on enabling 2FA here. For most people, I'd recommend using Authy with an SMS backup.
@Administrators
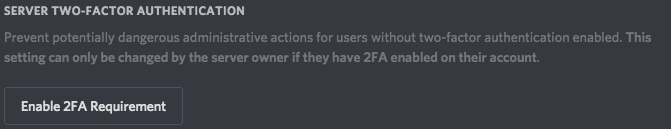
Assuming you've followed the above advice, you should now have 2FA enabled. Discord allows you to force this for your entire moderation team, and I would highly recommend doing so. This can be done on the "Moderation" tab of server settings.
Have I got something wrong, or have you got any suggestions for improvements? Let me know at [email protected].